Last Updated on March 2, 2024
Modern business cannot exist without computer and information technologies. Any company at different stages of the business processes different sorts of informational data. Company information is available to company employees, and it is usually stored on cloud services, on the computers of these employees, on dedicated storage facilities or in databases.
Disruption of any system of a company as a result of a hacker attack can lead to a halt in business processes, in production and in the functioning of the company’s logistics. Any business lagging is a loss of revenue opportunities.
It is possible to avoid cyber security risks – to build the right cyber security system. Such a measure can protect the company’s business from leakage of information, unpredictable situations, and money lose.
Employees as the main threat

Personnel security is a complex and multi-layered system. The source of threats may be personnel who has access to confidential information and has the ability to use this information, as well as an inefficient information security system. The balance of interests of all participants in labor relations is a fundamental element in personnel security. The level of influence of a human factor on the information security of a company is different. Sometimes threats arise due to low qualifications of personnel, sometimes due to malicious intent, and sometimes due to unconscious mistakes of employees of the organization.
In order to ensure personnel security HR specialists can check such workers on interview. Every company employee and every possible candidate for a vacant position should first of all be considered as a possible source of security threat. Workers with low qualifications are very dangerous for a company, too. Also, the occurrence of risks is influenced by the absence of a clearly defined legal relations and inadequate assessment of results. An indicator of good organization of personnel security system is the prevention of losses and damages from workers.
Employers and security specialists should also conduct lectures on the question of internet security and what is website security with workers. The security of a company directly depends on the loyalty of the staff, how good the attitude of the company’s employees to the management and the organization as a whole is.
Security issues
1. Violation of confidentiality
A competitive company can get secret information about a new product, technological data and a marketing plan.
2. Violation of integrity
The risk of substitution of bank details in the database. As a result, the accounting department carries out the payment, and the money goes not to the accounts of suppliers, but to the accounts of intruders.
3. Violation of accessibility
The risk of completely blocking the operation of company information systems as a result of a virus attack.
Any of these violations can happen because of human factor of employees, or because of incorrect performance of protection systems.
Cybersecurity measures

Cybersecurity is the implementation of measures to protect systems and networks, also it’s development of software applications against cyber attacks. Cyber threats are aimed at gaining access to confidential information, its modification, and destruction, at stealing users’ money or at disrupting the normal operation of companies.
To secure your website you can address to a specialist for the development of a company’s personal website or individual software for a company, check this out to find more relevant information concerning security and development of a website.
Online security
Although it is not always possible to protect yourself from being chosen as a target for harassment on the Internet, some measures can be taken to reduce the risk for yourself and your company. Antivirus must be installed on the computer. Do not open files sent to the mailbox from unfamiliar addresses. Often viruses spread through attachments to emails. Opening an unfamiliar file can result in the theft of all data from your work computer.
Check how complicated your password is. A unique and complex password to email, data cloud, and work chat – the key to online security. Online password generator can also be used for producing a reliable password for a system.
Technologies
Technology is an essential element, providing organizations and individual users with the tools they need to protect against cyber attacks. The main components that need to be protected are computers and smart devices; network and cloud environment. The most common technologies are developed to protect the listed components include firewalls of new generation, DNS filtering, antivirus software, malware protection, and personal email protection.
There are no 100% secure technologies, whether you use Mac iOS or Windows. Business Insider reports, that even such a precautious system as Apple can’t provide powerful cybersecurity protection, so each user should take all the necessary measures to avoid ruining results of cyber attacks.
Best internet security software
They say that the best internet security software is the one which costs money. We recommend your company invest in the security of its database and information, and the best way to ensure it – buy and install reliable antivirus software for every computer in an office.
Secure browsing
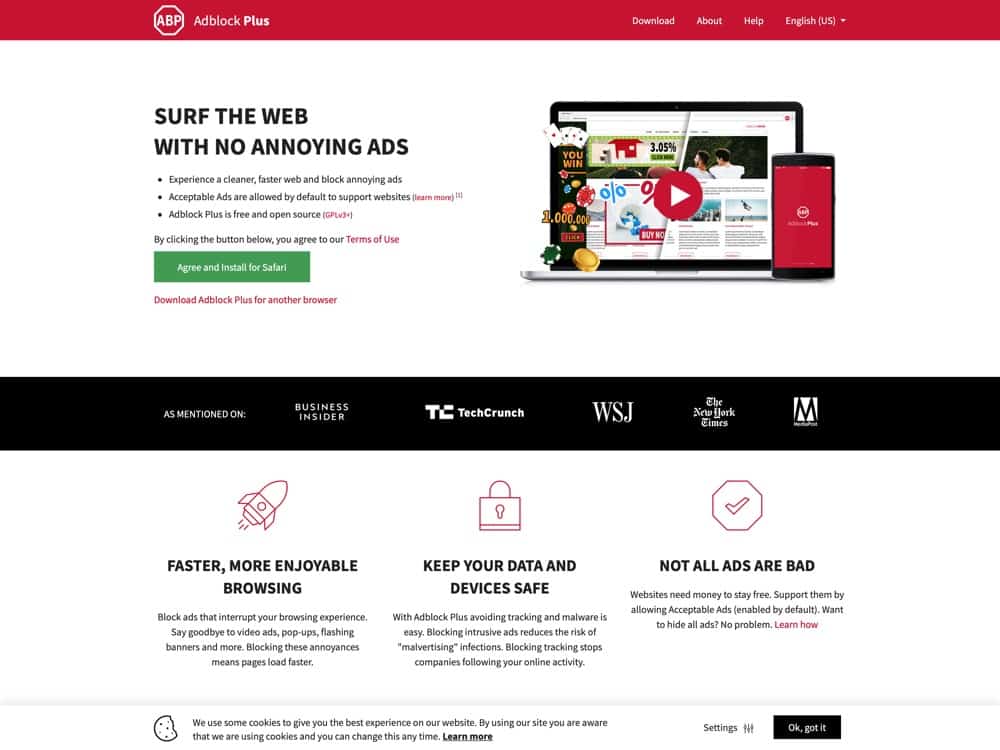
Use a tool that scans traffic and limits your access to infected web pages. Do not click on suspicious links, applications or abbreviated links that you do not know where they go. Do not go to sites that host illegal content – torrents, for example. There are blocking programs which reduce the risk of installing malware, be sure to instal it for a proper protection.
Important detail – Always Back Up.
Most of the attacks aimed at stealing files are automated, which means that anyone can become a victim. If your computer has outdated browsers, plug-ins or applications, and you have files, they can be stolen. Modern cybersecurity issue is malware that blocks your files and requires a ransom for it.
Bottom Line
The information has a great value for a company of any scale; therefore, it must be protected and properly stored. Different information has a different value for the company, and its loss eventually leads to loss of money and time. Leakage of information about the main business owners may provoke a threat of a raider seizure of the company. It is necessary to ensure the protection of assets, local network data of computers and servers.
Cybersecurity includes close attention to personnel, loyalty in communication with employees and proper check of any individual who works for you. Want to protect your company and its employees? Get to creating a reliable cyber security system.

